Stop PII Leaks Before They Happen - Right in Your Code

The Problem
PII Leaks Are Sneaky, Costly, and Often Caught Too Late
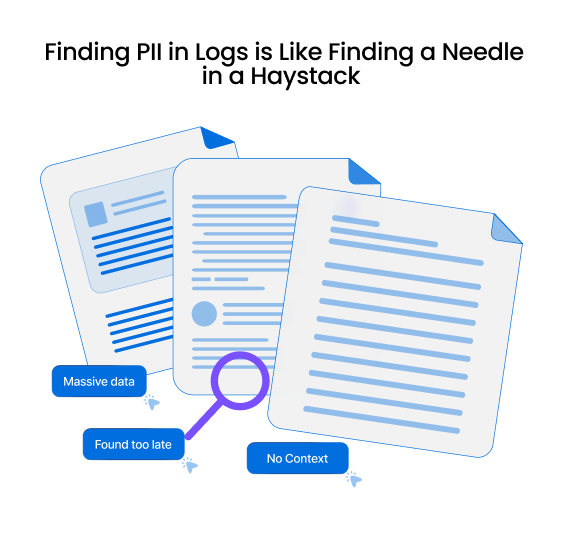
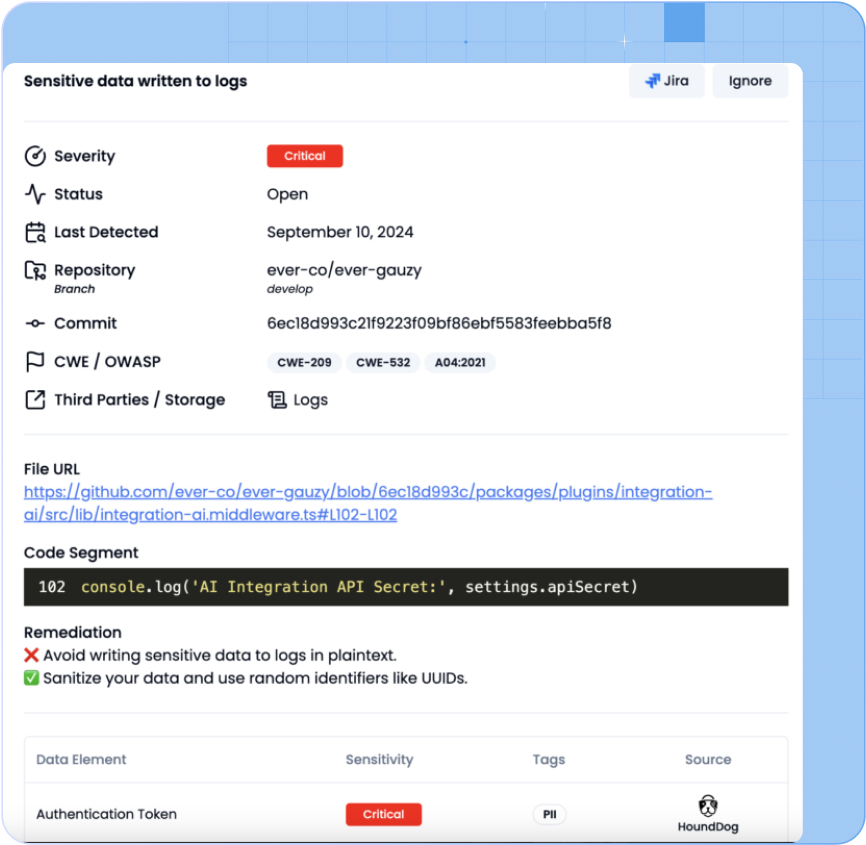
PII Overlogging & Oversharing. Developers unintentionally overlog and overshare PII across risky mediums such as logs, files, and third-party integrations. As teams grow, this risk escalates.
DLP’s Reactive & Unreliable Detection. Relying solely on DLP for PII detection in logs is reactive and unreliable due to sampling limitations. Issues are often identified too late—after logs have been ingested by multiple tools—without context on the root cause.
Data Sensitivity. AppSec teams struggle to prioritize risks effectively, relying on CVSS scores while neglecting data sensitivity. This leads to improper prioritization of vulnerabilities in code.
Privacy & Compliance Teams Struggle to Keep Up With Rapid Product Development
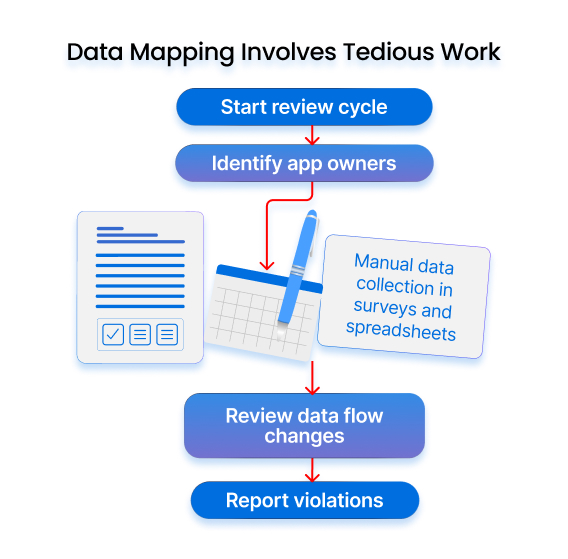
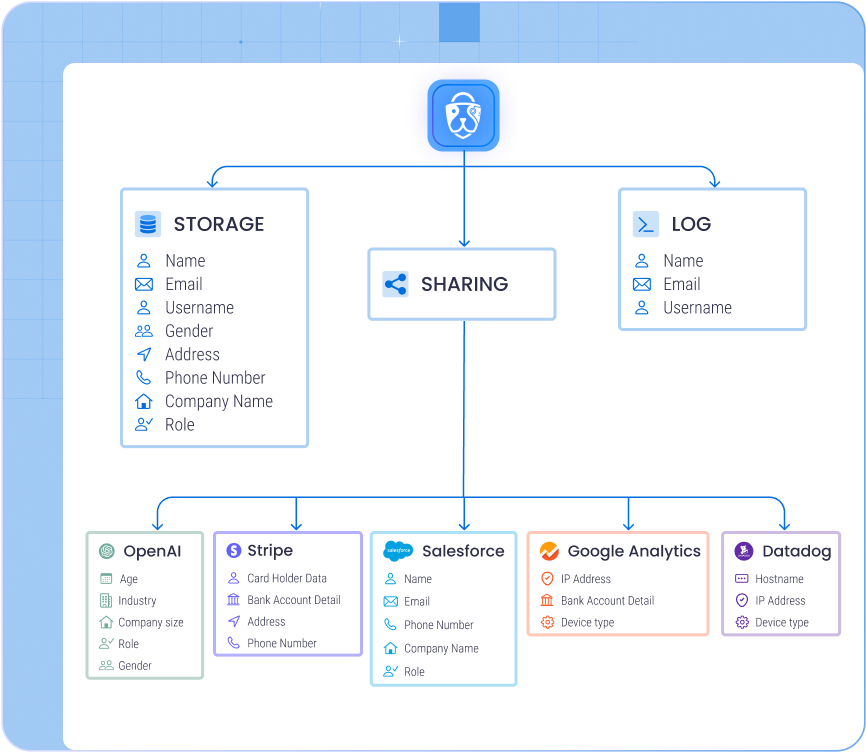
Manual Data Mapping Can’t Keep Up. Compliance teams rely on tedious surveys and spreadsheets, resulting in incomplete and outdated data maps that fail to reflect the latest code updates.
Third-Party Data Blind Spots. Most organizations lack visibility into the types of PII shared with third-party integrations, increasing the risk of unnoticed leaks and DPA violations.
AI Exacerbates PII Risk. AI applications introduce multiple interaction points and abstraction layers, making tracking and controlling sensitive data exposure even more challenging.
The Solution
Start PII Leak Detection And Data Flow Mapping Where It Matters Most: In the Code
HoundDog.ai for Proactive Sensitive Data Protection
-
Eliminate the chaos of reactive cleanups by enforcing privacy-by-design from day one, enabling proactive data minimization, and moving one step closer to an “Assume Breach” posture.
-
Expand AppSec coverage to detect unintentional developer mistakes that lead to overlogging and oversharing of sensitive data—issues that are difficult to identify and remediate in production—reducing the burden on your data security peers.
-
Enhance risk scoring by factoring in the sensitivity of data processed within application codebases - not all SQL injection vulnerabilities should be treated equally.
HoundDog.ai for Privacy Compliance Automation
-
Privacy by design can be overwhelming - we’re here to help.
-
Evidence-based data mapping & visualization. Track PII, PHI, and CHD data flows across all storage mediums and third-party integrations. Maintain a continuously updated PII inventory at the pace of development, with visual proof of where data is stored, shared, and processed.
-
Proactive detection of DPA violations. Catch data processing agreement (DPA) violations caused by sensitive data oversharing with third-party integrations early—avoiding costly production issues
-
Automated RoPA, PIA, and DPIA generation
-
New PII/PHI alerting. Get real-time alerts when new PII/PHI data elements are introduced to the codebase, categorized by sensitivity level.
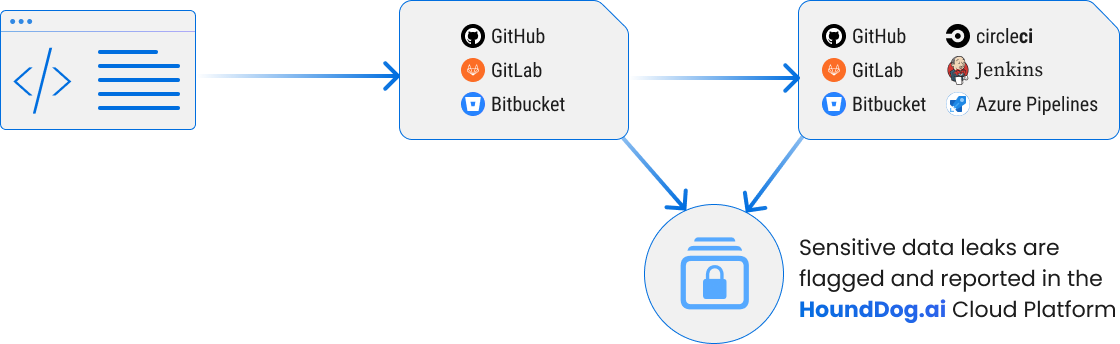
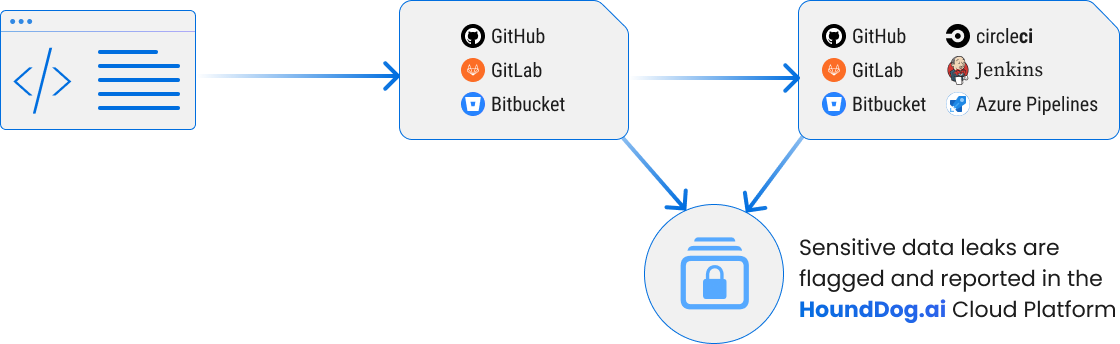
Enabling PII Leak Detection & Data Mapping Across All Stages of Development
IDE PLUGINS. (VS Code IntelliJ and Eclipse)
- Highlights PII leaks as code is being written
Managed Scans
- Offload scanning to HoundDog.ai with direct source control integrations
CI/CD Integrations
- Integrate the scanner into CI pipelines for pre-merge checks.
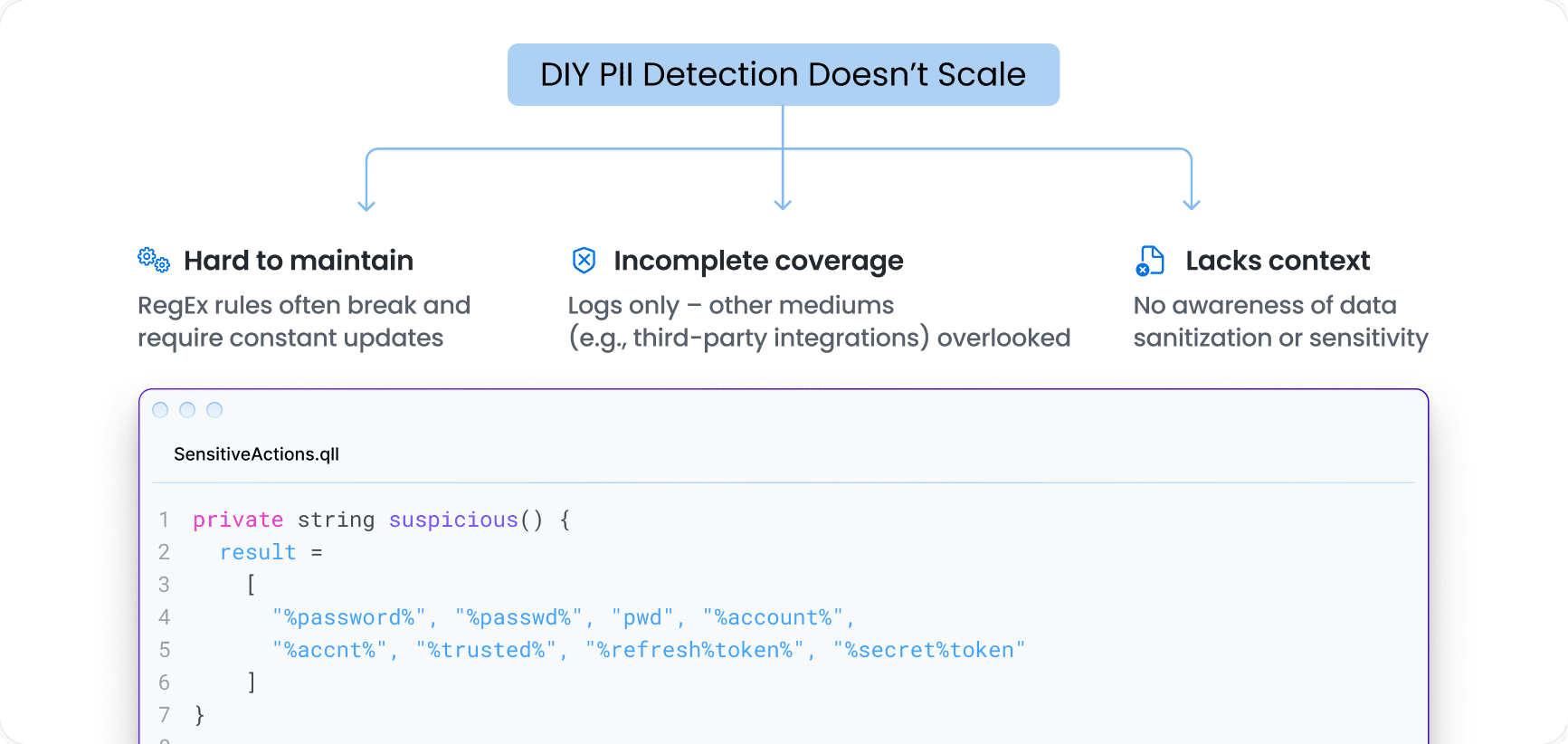
DIY PII Detection Doesn’t Scale
Hardcoded RegEx rules break easily and are a nightmare to maintain. Most DIY efforts stall before they scale
HoundDog.ai: Purpose-Built for PII Detection & Data Mapping
Unparalleled Coverage and Accuracy
Built-in detection with extensive coverage across:
- Sensitive data elements (PII, PHI, PIFI, CHD)
- Risky data sinks (including hundreds of third-party integrations)
- Sanitization functions (flag only when data isn’t properly sanitized)
Endless Flexibility
- Finetune detection across data elements, sinks, and sanitization to fit your environment.
Ready to Scale
- Connect to GitHub, GitLab, or Bitbucket to scan code, block PRs, and leave actionable comments—automatically.
- Managed Scans: Offload scanning to HoundDog.ai for continuous, hands-off coverage
- CI Jobs: Push CI configs to selected repos using your self-hosted runners, with options for direct commits or approval-based PRs
AI-Ready
- AI-powered detection that plugs into any LLM running in your environment—boosting coverage across data elements, sinks, and sanitization, while minimizing manual tuning. (Coming in Q2 2025)
Return On Investment
ROI for Proactive Sensitive Data Protection
ROI for Automated Privacy Compliance
Sensitive Data Protection at the Speed of Development
Juvare
Make Privacy-by-Design a Reality in Your SDLC
Shift Left on Privacy. Scan Code. Get Evidence-Based Data Maps. Prevent PII Leaks in Logs and Other Risky Mediums Early—Before Weeks of Remediation in Production.