Data Minimization and PII Leak Prevention
Shift-left sensitive data protection that prevents PII leaks at the source and enforces data minimization at the code level
Prevent PII Leaks from the Source
Weeks lost chasing sensitive data across application logs?
Not anymore. HoundDog.ai flips the model by analyzing code early to catch unintentional developer mistakes that lead to the overlogging and oversharing of sensitive data, before it ever reaches production.
Third-party risk management starts with visibility
from simple_salesforce
import Salesforce
from hubspot
import HubSpot
from amplitude
import Amplitude, BaseEvent

Uncover all third-party and shadow integrations introduced by engineering teams, sometimes without the knowledge or approval of privacy teams
from datadog
import DogStatsd
import sentry_sdk
import analytics

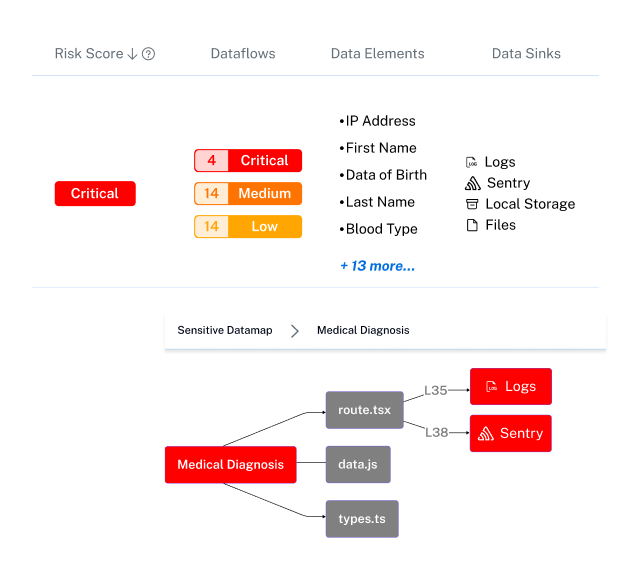
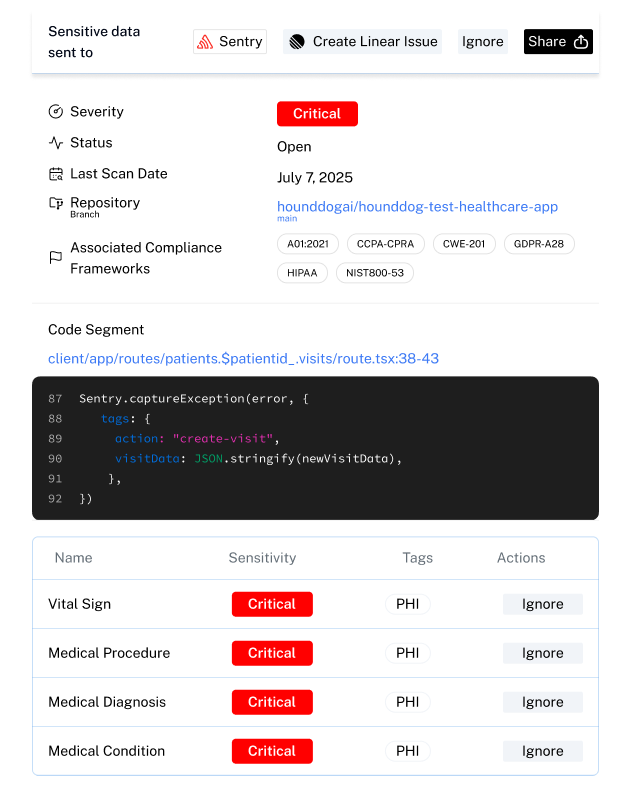
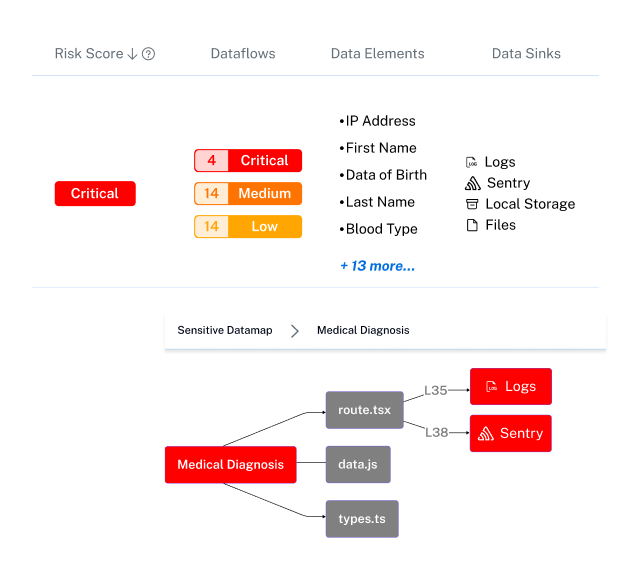
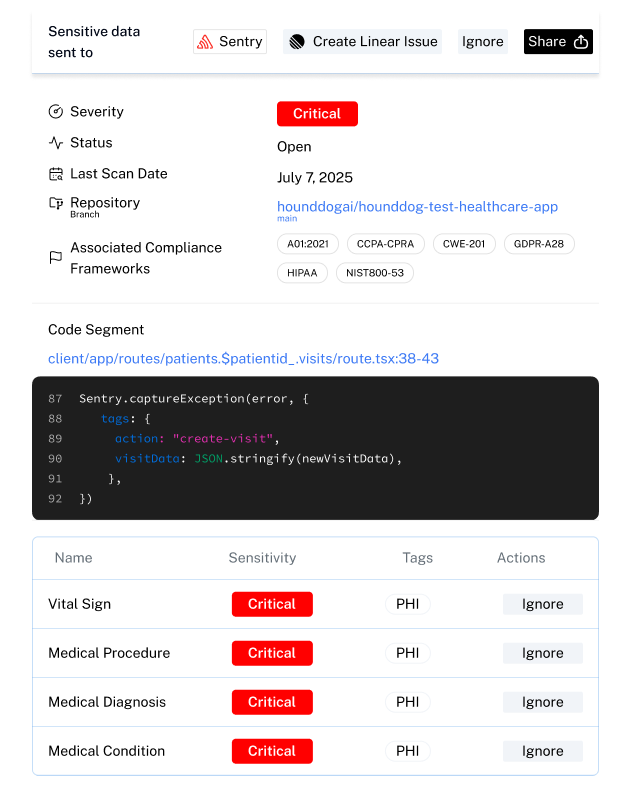
Track sensitive data across code to prevent PII leaks



Detect developer (or AI-generated) mistakes that leak sensitive data into logs, files, local storage, and other risky areas.
Logs
Files
Local Storage
Cookies
JSON Web Tokens
Enforce privacy rules and stop risky code before it reaches production

Preventing Sensitive Data Leaks From Developer Oversights Like Logging Full Objects Or Passing Tainted Variables Before Applications Go Live
Proactive Third-Party Risk Management and Shadow IT Discovery
Disadvantages of Current Approaches:
Most platforms rely on identity providers or network traffic to detect third-party integrations, which only reveals tools that have already been authorized or are actively used.
These methods miss SDKs, open-source packages, and homegrown integrations embedded directly in code, leaving security teams blind to Shadow IT.
Advantages of HoundDog.ai's Approach:
HoundDog.ai discovers third-party SDKs and APIs directly in the codebase before they are deployed or granted access to data.
This early detection gives security and privacy teams full visibility into both sanctioned and unsanctioned third-party integrations across the development lifecycle.
Shadow integrations are surfaced as part of the CI workflow, making it easy to block risky code before it leads to compliance or security issues.
Proactive Third-Party Risk Management and Shadow IT Discovery
Disadvantages of Current Approaches:
Most platforms rely on identity providers or network traffic to detect third-party integrations, which only reveals tools that have already been authorized or are actively used.
These methods miss SDKs, open-source packages, and homegrown integrations embedded directly in code, leaving security teams blind to Shadow IT.
Advantages of HoundDog.ai's Approach:
HoundDog.ai discovers third-party SDKs and APIs directly in the codebase before they are deployed or granted access to data.
This early detection gives security and privacy teams full visibility into both sanctioned and unsanctioned third-party integrations across the development lifecycle.
Shadow integrations are surfaced as part of the CI workflow, making it easy to block risky code before it leads to compliance or security issues.

Data Minimization and Leak Prevention
Disadvantages of Current Approaches:
Advantages of HoundDog.ai’s Approach:
Built for AppSec Teams and Loved by Developers

For Developers
For AppSec Teams
Enabling PII Leak Detection & GDPR Data Mapping Across All Stages of Development
IDE Plugins
Detect sensitive data leaks directly in your IDE as you write code.
Catch privacy risks early before they reach production.
Managed Scans
Offload scanning to HoundDog.ai with direct source control integrations.
Automatically analyze repositories for privacy risks.
CI/CD Integrations
Use HoundDog.ai source control integrations to auto configure CI.
Block risky pull requests before they are merged.
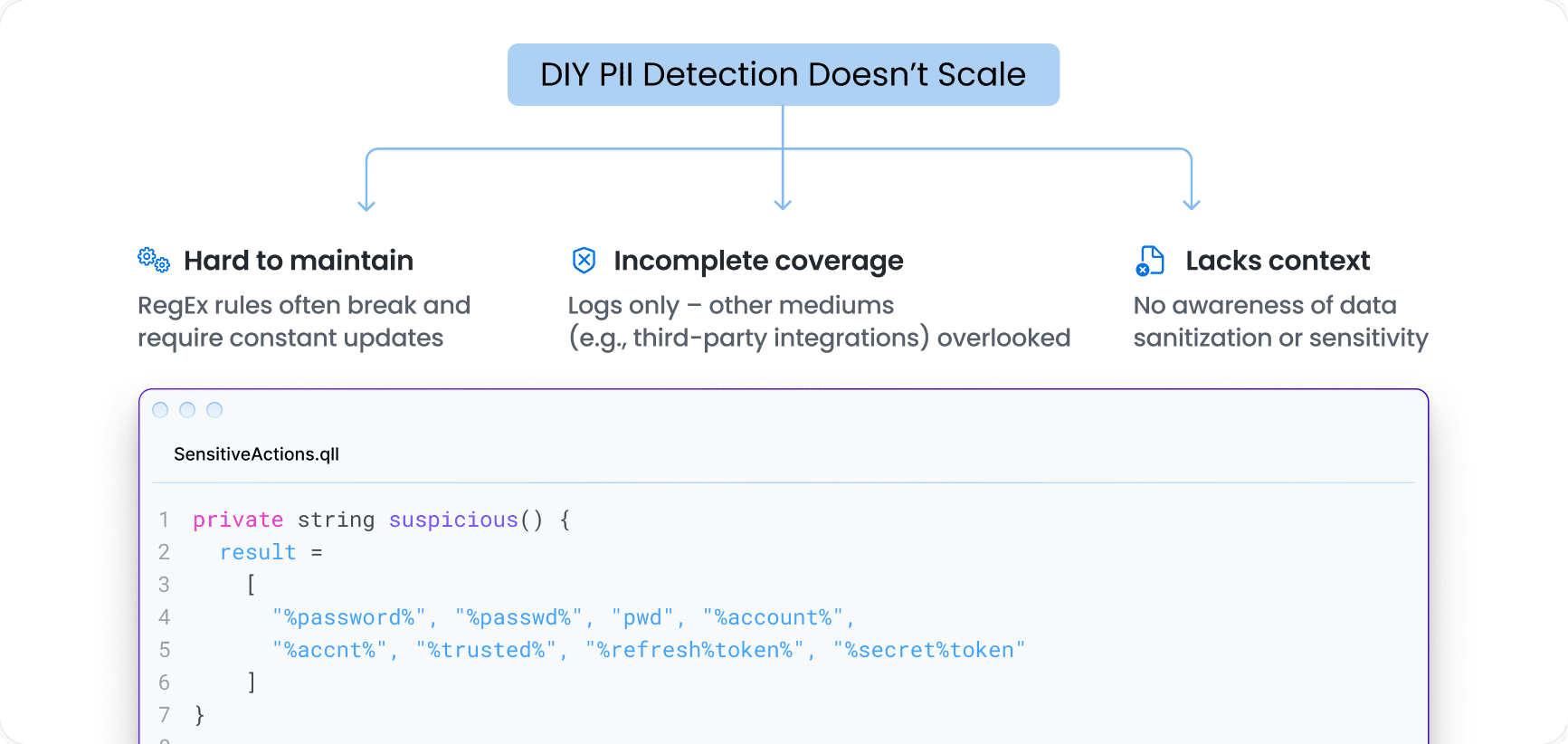
DIY PII Detection Doesn’t Scale
Hardcoded RegEx rules break easily and are a nightmare to maintain. Most DIY efforts stall before they scale
HoundDog.ai: Purpose-Built for PII Detection & Data Mapping
Unparalleled Coverage and Accuracy
Built-in detection with extensive coverage across:
- Sensitive data elements (PII, PHI, PIFI, CHD)
- Risky data sinks (including hundreds of third-party integrations)
- Sanitization functions (flag only when data isn’t properly sanitized)
Endless Flexibility
- Finetune detection across data elements, sinks, and sanitization to fit your environment.
Ready to Scale
- Connect to GitHub, GitLab, or Bitbucket to scan code, block PRs, and leave actionable comments – automatically.
- Managed Scans: Offload scanning to HoundDog.ai for continuous, hands-off coverage
- CI Jobs: Push CI configs to selected repos using your self-hosted runners, with options for direct commits or approval-based PRs
AI-Ready
- [Coming Soon] AI-powered detection that plugs into any LLM running in your environment – boosting coverage across data elements, sinks, and sanitization, while minimizing manual tuning.
Realize Significant Cost Reduction and Increased Productivity
ROI for proactive sensitive data protection
Why Shift-Left Privacy Matters
Stop privacy risks at the source — while code is being written, not after it reaches production.
AI Exposure Happens Fast
Sensitive data can be exposed to AI tools
within minutes of code changes.
Post-Production Tools Are Too Late
Fixing leaks after release
doesn’t prevent real damage.
Compliance Requires Prevention
Modern privacy programs must prevent risks,
not just report them after exposure.
Trusted by Replit to detect privacy leaks across AI generated applications built by more than 45 million creators.
Make Privacy-by-Design a Reality in Your SDLC
Shift left on privacy with code scanning. Detect PII leaks, map sensitive data flows, and generate GDPR data maps, RoPA, PIA, and DPIA before code reaches production.