Privacy Code Scanner and API Context Engine for AI Coding Agents
Detect PII leaks, automate GDPR data mapping with a continuously updated RoPA, validate privacy reviews with code-level evidence, and give AI coding agents real-time API context.
Two Products. One Platform.
Comprehensive visibility into privacy risks in your application code with automated GDPR data mapping and real time insight into API dependencies for AI coding agents across your services.
Embed privacy into development to detect privacy risks early and automate GDPR data mapping, RoPA, PIA, and DPIA reporting.
No surveys. No spreadsheets. No relying on memory.
Provide AI coding agents with continuously updated API dependency graphs and service context across large monorepos and complex microservice architectures.
Safe API changes. Faster development. Lower AI token costs.
Automated gRPC documentation and API context
The gRPC documentation problem
- Protobuf files define your schemas – but that’s only half the picture
- Which services consume which APIs? Which fields are actually used? Neither lives in .proto files
- Developers end up grepping codebases or pinging teammates on Slack to find out
- Documentation goes stale the moment someone ships a new consumer
How HoundDog.ai API Context Engine solves it
- Analyzes both your .proto files and your service code
- Produces a live, accurate map of every gRPC API, every consumer, and every field in use
- Works as a gRPC service discovery layer for your team
- Acts as a context source for any MCP-compatible AI coding agent – Cursor, Claude Code, Copilot, and more

Problem: Privacy Risks Start in Code - Not After Deployment
Traditional privacy tools detect problems too late, when data is already in motion,
pushing teams into remediation rather than prevention.
Sensitive Data in Logs & Local Storage
- Sensitive data appearing in logs or local storage forces organizations into reactive cleanup.
- DLP tools surface problems only after exposure, sending teams into weeks of tracing data paths, cleaning up logs, and rewriting code.
- Incidents often start with simple oversights like printing full user objects or passing tainted variables into logging functions.
- As applications scale and code paths multiply, these mistakes become harder to catch and more frequent.
Shadow AI & Third-Party Integrations
- Data shared with third party or AI integrations must align with Data Processing Agreements and your privacy notice.
- Silent code changes can redirect sensitive fields to analytics platforms, observability pipelines, or LLM prompts.
- These hidden shifts erode user trust and increase regulatory exposure long before privacy teams are aware.
Hidden Cross-Service Flows
- Sensitive data flows between microservices and APIs in ways teams cannot easily track or document.
- Cross repo dependencies over REST, GraphQL, or gRPC and complex code transformations defeat traditional scanning approaches.
- As a result, sensitive data exposed through these API protocols often goes undocumented or poorly understood, creating hidden privacy and compliance risk.
Sensitive Data in AI Prompts
- AI usage is accelerating, increasing the risk of unintentionally sharing sensitive data with external models.
- Many companies restrict AI services, yet scans routinely uncover AI SDKs like LangChain or LlamaIndex.
- Current privacy tooling is either too reactive, discovering these flows after the fact, or completely blind to them.
- Privacy teams scramble to understand what data is sent to AI systems and whether user notices and legal bases cover those flows.
Why Existing Tools Fail
Regulations like GDPR and US privacy frameworks require accurate data maps and reports such as RoPA, PIA, and DPIA. In fast moving engineering environments, those maps quickly fall out of date.
Most data privacy solutions fall into two buckets.

Governance, Risk, and Compliance Platforms

Production focused Privacy Platforms

How Privacy Code Scanning Works
Detect sensitive data flows, prevent PII leaks, and automate GDPR data mapping directly in your development workflow.
Scan Code as It’s Written
HoundDog.ai integrates directly into your development workflow to scan code in IDEs (VS Code, IntelliJ, Cursor) and in CI pipelines as it is written or generated.
Trace Sensitive Data Flows
Automatically map sensitive data flows directly from source code across functions, APIs, third party services, and AI integrations to detect privacy risks and support GDPR data mapping.
Enforce Privacy Rules Before Deployment
Apply allowlists to define which data types are permitted in LLM prompts and other risky sinks, and automatically block unsafe pull requests to maintain compliance.

Build Customer Trust with Transparent Data Handling and GDPR Data Mapping
- Automatically generate GDPR data mapping and data flow maps directly from source code to show where sensitive data is collected, processed, and shared across functions, APIs, third party services, and AI integrations.
- Keep your Org RoPA continuously updated with new data flows and subprocessors surfaced as suggested edits at the speed of development – giving privacy teams a centrally managed record across all processing activities, not just custom apps.
- Auto-generate audit-ready App RoPAs, Privacy Impact Assessments (PIA), and Data Protection Impact Assessments (DPIA) pre-populated with detected sensitive data flows and privacy risks, aligned with GDPR, CCPA, HIPAA, and other regulatory frameworks.
- Validate privacy reviews with code-level evidence before code ships – ensuring what was approved at the design stage is consistent with what was actually implemented.
- Detect sensitive data flows using privacy code scanning to give privacy and security teams continuous visibility into processing activities without surveys, spreadsheets, or manual discovery.

What Makes HoundDog.ai Different
Purpose built for engineering teams that need to detect sensitive data flows and automate GDPR data mapping directly from source code.
Code-Level Data Flow Intelligence
Detect and map sensitive data flows directly from source code across APIs, services, and third party integrations without relying on surveys, spreadsheets, or privacy tools that miss hidden integrations and SDKs.

Built for AI & LLM Workloads
Discover AI SDKs embedded in code and detect sensitive data flows to LLM prompts and external AI APIs before your apps go live.

Prevent Risk Before Deployment
Catch PII leaks and risky data flows during development and code review, not after data has already been logged, shared, or leaked.

Enabling PII Leak Detection & GDPR Data Mapping Across All Stages of Development
IDE Plugins
Detect sensitive data leaks directly in your IDE as you write code.
Catch privacy risks early before they reach production.
Managed Scans
Offload scanning to HoundDog.ai with direct source control integrations.
Automatically analyze repositories for privacy risks.
CI/CD Integrations
Use HoundDog.ai source control integrations to auto configure CI.
Block risky pull requests before they are merged.
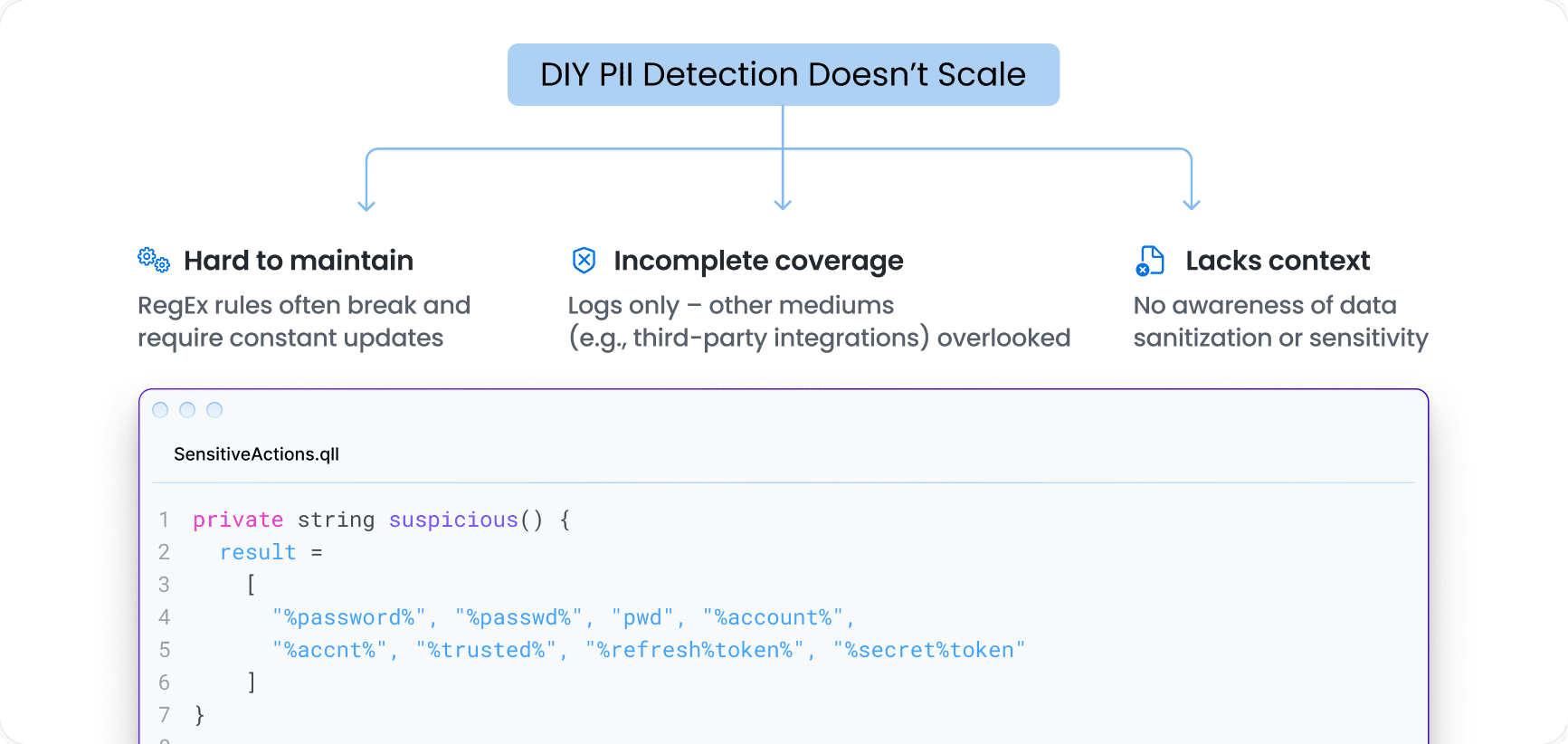
DIY PII Detection Doesn’t Scale
Hardcoded RegEx rules break easily and are a nightmare to maintain. Most DIY efforts stall before they scale
Built for Enterprise-Grade Security
Designed to meet the requirements of large, security-conscious organizations.
Built for Enterprise Teams
- Trusted by Replit, running 10,000+ privacy scans per day to help 45M creators bake privacy into the earliest stages of prototyping and app creation
- Used by Fortune 1000 companies across technology, healthcare, and finance
- SOC 2 compliant, with a transparent Trust Center offering access to the latest SBOM and penetration testing reports
- Hands on, highly responsive customer support
Secure by Default
- No production data or runtime ingestion required
- Runs locally in your environment or CI pipelines
- Secure broker for self hosted source control systems that meets strict network and data handling standards
- Transparent Trust Center with up to date SBOM and penetration testing reports
Return On Investment
ROI for Proactive Sensitive Data Protection
ROI for Automated Privacy Compliance
Why Shift-Left Privacy Matters
Stop privacy risks at the source — while code is being written, not after it reaches production.
AI Exposure Happens Fast
Sensitive data can be exposed to AI tools
within minutes of code changes.
Post-Production Tools Are Too Late
Fixing leaks after release
doesn’t prevent real damage.
Compliance Requires Prevention
Modern privacy programs must prevent risks,
not just report them after exposure.
Trusted by Replit to detect privacy leaks across AI generated applications built by more than 45 million creators.
Make Privacy-by-Design a Reality in Your SDLC
Shift left on privacy with code scanning. Detect PII leaks, map sensitive data flows, and generate GDPR data maps, RoPA, PIA, and DPIA before code reaches production.
